I am using the Docker container from Linuxserver for my instance of DokuWiki. This post is about enabling OpenLDAP and the local admin account for authentication. I am using Univention Corporate Server (UCS) as my OpenLDAP server. You can use any other LDAP server such as FreeIPA, ClearOS, Turnkey Linux OpenLDAP, Microsoft Active Directory, etc. Any of these will do the job, I just use UCS for my other use cases.
We would need a LDAP service account for DokuWiki. This account can be just a regular domain user. I am using the Univention, yours will be different, but the concept should be the same. In Univention, login to the web UI and navigate to Users
- Click on Add
- From the Container drop-down menu, select /users
- Click on NEXT
- Fill-out the service account info. In UCS, the required fields are the Last name and User name
- Last name: dokuwiki_svc
- User name: dokuwiki_svc
- Click NEXT
- Enter the service account’s password
- Click CREATE USER as shown in Figure 1
- Click Cancel at the next window

Not shown in this post, but I tend to add my service accounts to another group that I created. This is optional, but I like it to organize my groups.
To pull the necessary LDAP information, SSH-in to the LDAP server and run the following command. Adjust the parameters based on your environment.
- -x # used simple authentication
- -h # ldaphost
- -D # bind dn
- -w # password of bind dn
- -b # search base
- localhost:7389 # Univention uses 7389 for LDAP. You can drop the port number
ldapsearch -x -h localhost:7389 -D "uid=admin,cn=users,dc=networkshinobi,dc=com" -w "password" -b "dc=domain,dc=tld" | grep dokuwiki # dokuwiki_svc, users, networkshinobi.com dn: uid=dokuwiki_svc,cn=users,dc=networkshinobi,dc=com cn: dokuwiki_svc uid: dokuwiki_svc krb5PrincipalName: [email protected] displayName: dokuwiki_svc gecos: dokuwiki_svc sn: dokuwiki_svc homeDirectory: /home/dokuwiki_svc uniqueMember: uid=dokuwiki_svc,cn=users,dc=networkshinobi,dc=com memberUid: dokuwiki_svc memberUid: dokuwiki_svc uniqueMember: uid=dokuwiki_svc,cn=users,dc=networkshinobi,dc=com
Based on the output, what we need is the dn output in line number 4, so make sure to jot this one down. We will need this info later. For now, close the SSH session from the LDAP server.
Login to DokuWiki web UI and navigate to Admin settings > Extension Manager > Search and Install
- In the Search Extension field, search for the plugin LDAP Auth Plugin by Andreas Gohr as shown in the Figure 2
- Click on Install to install the plugin

While still in Search and Install page, we will install another plugin to allow us to chain login from LDAP or local account. We are going to use the authentication chaining, so that we can still use the local admin account.
- In the Search Extension field, search for the plugin chained auth plugin by Philipp Neuser, Christian Marg, Pawel Jasinski as shown in Figure 3
- Click on Install to install the plugin

Navigate back to Admin settings > Configuration Settings. On the right side of the page, you will see the Table of Contents as shown in Figure 4. What we need to configure are the following :
- Authentication
- Authldap
- Chained authentication plugin
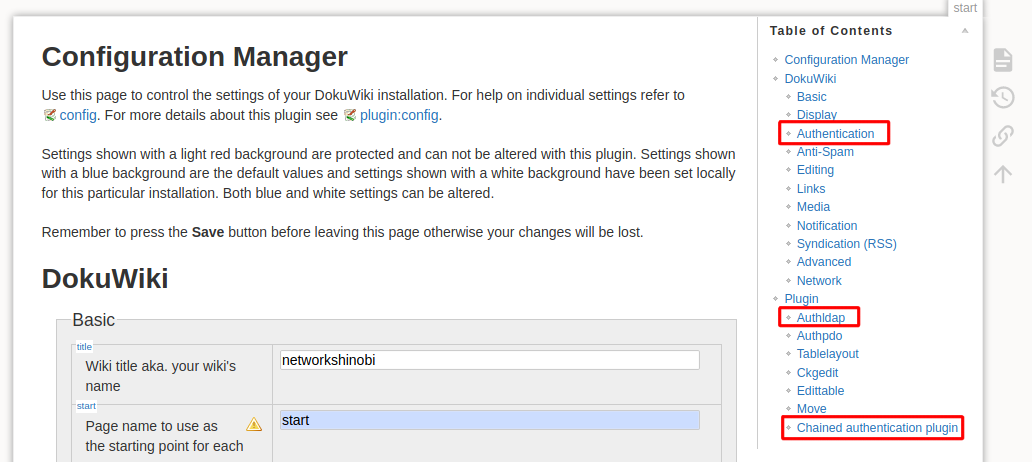
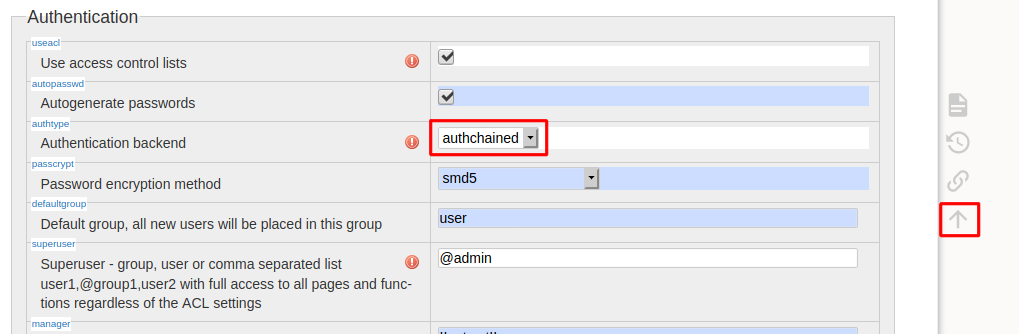
- From the Table of Contents, click on Authentication. This will jump us to the Authentication section
- Select authchained from the Authentication backend drop-down menu
- Click on Back to Top arrow to return us back to the Table of Contents
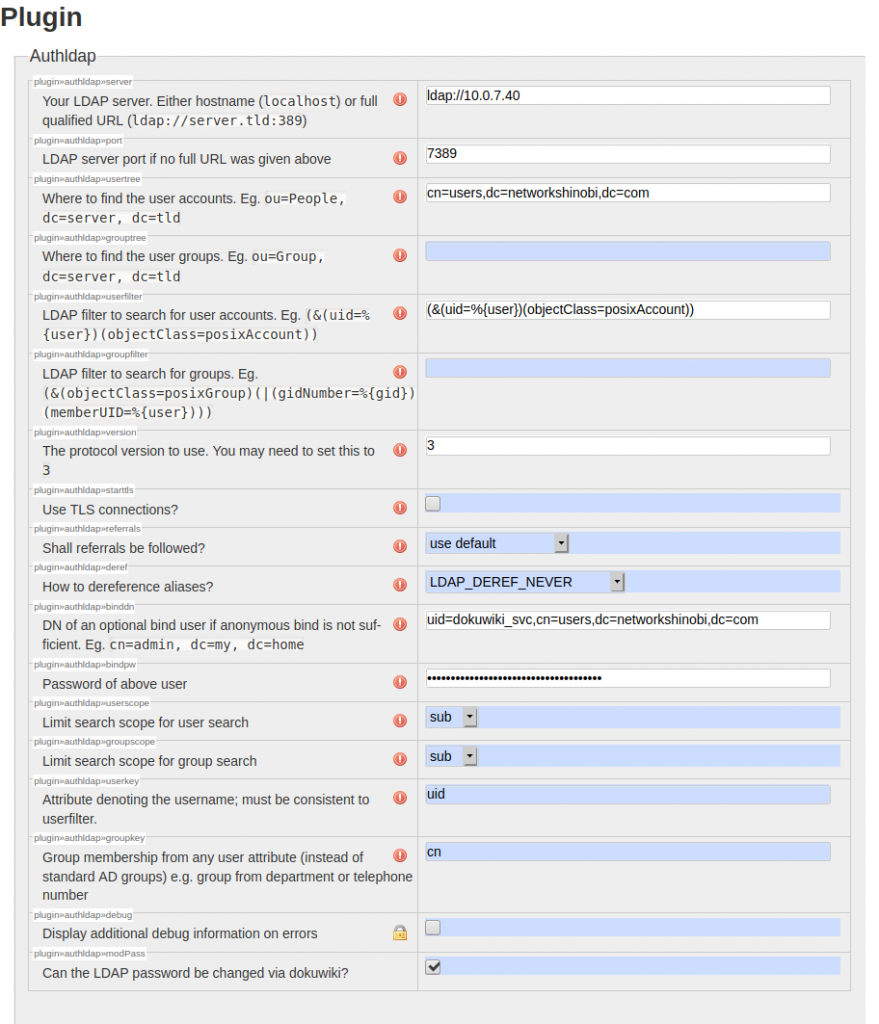
- From the Table of Contents, click on Authldap. This will jump take us to the Plugin section
- Enter the hostname or IP address of the LDAP server in the Your LDAP server field. Make sure that add ldap:// before the IP address or hostname
- Enter the LDAP server port in the LDAP server port field. For LDAPS, enter the LDAPS port. See Figure 7
- Enter the base DN in the Where to find the user accounts field. This is the dn from line number 4, but remove the uid section
- Copy the sample from LDAP filter to search for user accounts and paste it to its field
- Change the protocol version to 3 in the The protocol version to use field
- Enter the whole dn value we jotted down from ldapsearch output line number 4 in the DN of an optional bind user field
- Enter the password of the bind DN (password of the service account) in the Password of above user field
- Leave every else in this section to the default value as shown in Figure 6
- Click on the Back to Top arrow to return back to the Table of Contents

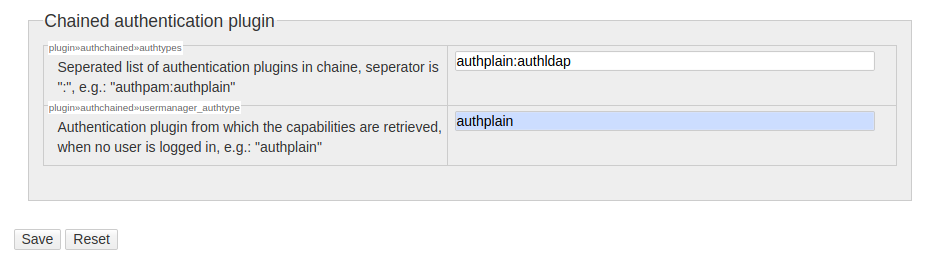
Once back to the Table of Contents, click on Chained authentication plugin. This should take us at the very bottom of the Configuration Page. From here, enter the following:
- Enter authplain:authldap in the Seperated list of authentication plugins … field
- Enter authplain in the Authentication plugin … field
- Click Save
At this point, LDAP authentication should work. Try to logout, and login using any users from your domain. You can also modify this information via CLI. If you are using the Linuxserver Docker container, it is located in /appdata/dokuwiki/dokuwiki/conf/local.php.
I hope you will find this helpful. Cheers!
